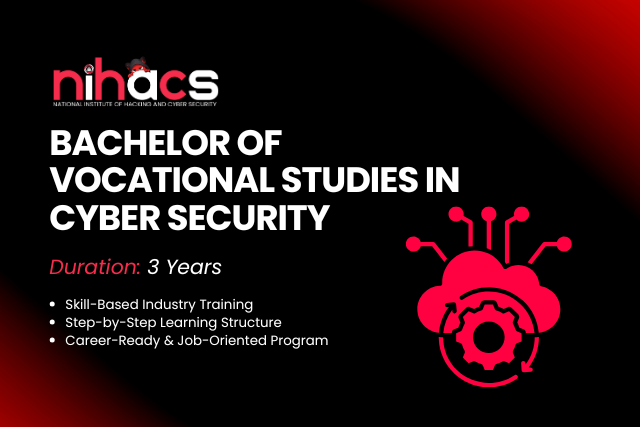
Courses Designed for the Real-World
Start your journey with our top-rated courses. Perfect for beginners and professionals alike.

Web Penetration Testing And Bug Bounty Hunting
Hands-on labs covering pen-testing, recon, and exploitation.

Transform Your Career in Cybersecurity
Join thousands of professionals who transformed their careers with our industry-leading cybersecurity course
OUR CAMPUS
Experience world-class infrastructure and facilities designed to nurture excellence

Our Campus
Where excellence meets innovation

Modern Library
State-of-the-art learning resources

Student Life
Vibrant community & culture

Smart Classrooms
Technology-enabled learning

Corporate Environment
World-class athletic facilities
See Where Our Security Experts Are Deployed
We focus on real-world penetration, not just certification. Threat intelligence labs, red team operations, and SOC rotations help you convert offers faster.
Where our security researchers now defend
Companies where our students work
































































Why Choose Us?
Industry-Led Training
Learn from professionals working in Fortune 500 companies and leading security firms with real-world experience and cutting-edge methodologies.
98% Placement Success
Join elite graduates securing positions within 90 days at top security firms with our proven track record and dedicated placement assistance.
State-of-the-Art Labs
Advanced cybersecurity labs with real attack scenarios and live threat simulations to master defensive and offensive security techniques.
150+ Industry Partners
Direct connections with CrowdStrike, Palo Alto Networks, Fortinet and more for internships, mentorship, and guaranteed job opportunities.
Hands-On Practical Training
80% practical, 20% theory approach with live projects, capture-the-flag competitions, and real-world penetration testing scenarios.
24/7 Career Support
Lifetime career guidance, resume building, interview preparation, and job search assistance even after graduation to ensure your success.
Certification Programs
Industry-recognized certifications including OSCP, CEH, CISSP, and CompTIA Security+ included in curriculum with exam preparation.
Flexible Learning Options
Choose from full-time, part-time, or self-paced online courses with weekend batches and evening classes to fit your schedule and commitments.
Industry-Led Training
Learn from professionals working in Fortune 500 companies and leading security firms with real-world experience and cutting-edge methodologies.
98% Placement Success
Join elite graduates securing positions within 90 days at top security firms with our proven track record and dedicated placement assistance.
State-of-the-Art Labs
Advanced cybersecurity labs with real attack scenarios and live threat simulations to master defensive and offensive security techniques.
150+ Industry Partners
Direct connections with CrowdStrike, Palo Alto Networks, Fortinet and more for internships, mentorship, and guaranteed job opportunities.
Hands-On Practical Training
80% practical, 20% theory approach with live projects, capture-the-flag competitions, and real-world penetration testing scenarios.
24/7 Career Support
Lifetime career guidance, resume building, interview preparation, and job search assistance even after graduation to ensure your success.
Certification Programs
Industry-recognized certifications including OSCP, CEH, CISSP, and CompTIA Security+ included in curriculum with exam preparation.
Flexible Learning Options
Choose from full-time, part-time, or self-paced online courses with weekend batches and evening classes to fit your schedule and commitments.
Cybersecurity FAQ
Essential answers to protect your digital assets and understand modern security threats
Two-Factor Authentication (2FA) is a security process that requires two different authentication factors to verify your identity. It combines something you know (password) with something you have (phone, security key) or something you are (biometric). This significantly reduces the risk of unauthorized access, even if your password is compromised. Studies show that 2FA can prevent up to 99.9% of automated cyberattacks.
The cybersecurity landscape continues to evolve with AI-powered phishing attacks, supply chain vulnerabilities, cloud security breaches, zero-day exploits, insider threats, and sophisticated social engineering. Ransomware-as-a-Service (RaaS) has made attacks more accessible to criminals. Mobile device compromises and IoT vulnerabilities are increasing. Deepfake technology is being used for fraud and manipulation. Organizations must stay vigilant and adopt proactive security measures.
Zero Trust is a security framework based on the principle 'never trust, always verify.' It assumes no user or device is trustworthy by default, whether inside or outside the network. Every access request is authenticated, authorized, and encrypted. Benefits include reduced attack surface, better visibility, improved compliance, and protection against insider threats. Given the rise of remote work and cloud services, Zero Trust is becoming essential for organizations of all sizes.
A Virtual Private Network (VPN) encrypts your internet connection, creating a secure tunnel between your device and the internet, masking your IP address and protecting data in transit—ideal for remote workers and public Wi-Fi. A firewall monitors and controls incoming/outgoing network traffic based on security rules, acting as a barrier between trusted and untrusted networks. Both serve different purposes: VPNs protect data privacy and location, while firewalls prevent unauthorized network access. Use both for comprehensive protection.
Act quickly to minimize damage: isolate affected systems to prevent spread, activate your incident response plan, preserve evidence for investigation, notify your cybersecurity team or managed service provider, change all compromised credentials, assess the scope and type of data affected, comply with legal notification requirements (GDPR, state laws), communicate transparently with affected parties, document everything for insurance and legal purposes, conduct a post-incident review, and implement remediation measures to prevent recurrence.
Protecting against ransomware requires a multi-layered approach: implement regular automated backups stored offline, keep all systems and software updated, use endpoint detection and response (EDR) solutions, train employees to recognize phishing attempts, segment your network to limit lateral movement, maintain robust access controls, and develop an incident response plan. Regular security audits and penetration testing can identify vulnerabilities before attackers exploit them.
Current cybersecurity best practices recommend changing passwords immediately if there's a suspected breach, rather than on a fixed schedule. Use unique, complex passwords for each account (minimum 12-16 characters with mixed case, numbers, and symbols). Password managers can generate and store these securely. Enable breach monitoring services that alert you when your credentials appear in data leaks. For high-value accounts, consider using passkeys or hardware security keys.
Phishing emails often exhibit red flags: sender addresses that mimic legitimate domains but have slight variations, urgent language creating false time pressure, requests for sensitive information, suspicious links (hover to preview URLs), poor grammar or formatting, unexpected attachments, and too-good-to-be-true offers. Always verify requests through official channels, use email filtering, enable link protection, and report suspicious messages. Security awareness training can reduce successful phishing by up to 80%.
Small businesses can implement effective cybersecurity on a budget: use free or low-cost tools (Windows Defender, open-source solutions), leverage cloud-based security services with pay-as-you-go pricing, prioritize employee training (the most cost-effective defense), implement basic hygiene (regular updates, strong passwords, backups), consider cyber insurance, use managed security service providers (MSSPs) for 24/7 monitoring at a fraction of in-house costs, and take advantage of government resources and grants for small business cybersecurity.
Biometric authentication (fingerprints, facial recognition, iris scans) offers strong security because biological traits are unique and difficult to replicate. However, they're not foolproof: biometrics can't be changed if compromised, sophisticated spoofing techniques exist, privacy concerns arise from biometric data storage, and false positives/negatives occur. Best practice: use biometrics as part of multi-factor authentication rather than the sole security method. Combine with passwords or security keys for maximum protection.